A Distributed Denial of Service (DDoS) attack is an attempt to make an online service unavailable by overwhelming it with traffic from multiple sources. Across the globe DDoS attack size, frequency and complexity is on the rise. At the same time, businesses have never been more connected and dependent on the availability of websites and online services. Many customer types are at risk, Broadcasters, Service Providers & Enterprises. DDoS is a problem that’s getting worse.
Implementation of a DDOS solution is not an easy task
When customers need to implement DDoS Mitigation Solutions into their network, they often have to perform major changes to the existing network in terms of deploying new Protocols (roll out MPLS, implement MPLS L3VPN) or having to redesign the complete network.
This article shows how to implement DDoS Mitigation with only minor impact on the Rest of the network, whilst reducing deployment time.
The Problem/Setup
Today more networks than ever need to implement DDoS Mitigation solutions in order to provide availability to their customers. Most solutions consists of two parts, an analysis machine (injector) which detects the attack and afterwards notifies the network that traffic needs to be Off-Ramped to the second part the washing or scrubbing appliance (scrubber). Once cleaned by the scrubber the traffic has to On-Ramped back to the network
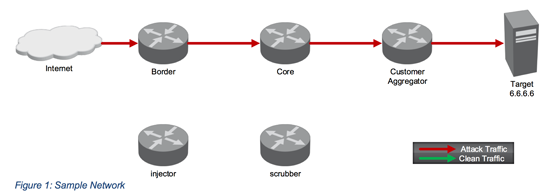
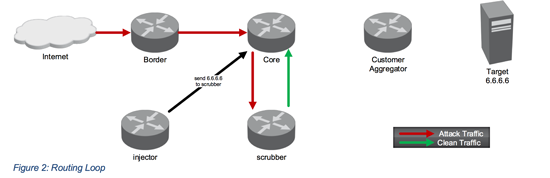
Figure 1 shows the normal flow of traffic during an attack. Let us move to figure 2, once an attack is detected the injector will notify the network that traffic needs to be send to the scrubber. The scrubber will clean the traffic and send the clean traffic back to the network. Unfortunately, the network was instructed to send all traffic directed to the target to the scrubber, which leads to a routing loop.
There are a couple of traditional approaches to solve that problem The options range from implementing varies kind of IP Tunnels (GRE, IPIP, IPSEC), using MPLS LSPs or deploy MPLS L3VPN (Clean VRF/Dirty VRF). We at Xantaro are happy to help our customers implementing these solutions and have done so many times.
Unfortunately, all of them lead to major changes in the existing network and sometimes to complete redesigns of the network. This costs time that usually cannot be spent when under attack often.
The innovative approach
As everybody is talking about SDN and OpenFlow, let us make use of these technologies to our advance without redoing the complete network.
The trick is that we still send the attack traffic (red) to the scrubber, it then passes a first OpenFlow Switch and is cleaned by the scrubber device and will return as clean (green) traffic. On its second run through the first OpenFlow switch, we transform green into blue traffic. The network knows that blue traffic needs to be forwarded to the Customer part of the network and does exactly that.
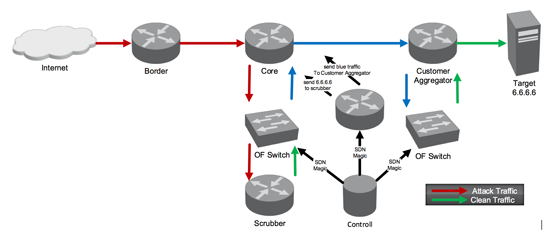
Once blue traffic has reached the Customer Part of the network, the network knows that this traffic has to be cycled through a second OpenFlow Switch. This second Switch transforms blue traffic back to green traffic and sends it back to the network.
Essentially, what happens to enable this trick is that we perform a distributed stateless Network Address Translation.
Part 2 to follow…The details of the solution
Share your opinion with us!
Your perspective counts! Leave a comment on our blog article and let us know what you think.
.png?width=300&height=300&name=Design%20ohne%20Titel%20(7).png)
